A vulnerability has been discovered that allows access to Microsoft BitLocker-protected drives using only files on a USB drive, without the recovery key.

A zero-day vulnerability called ' YellowKey ,' which could potentially bypass Microsoft's BitLocker-encrypted drives, has been disclosed by security researcher Nightmare-Eclipse. Alongside this, another zero-day vulnerability, ' GreenPlasma ,' which could lead to escalation to SYSTEM privileges, has also been revealed.
GitHub - Nightmare-Eclipse/YellowKey: YellowKey Bitlocker Bypass Vulnerability · GitHub
BitLocker bypass zero-day exploit released by disgruntled researcher | Cybernews
https://cybernews.com/security/researcher-releases-bitlocker-bypass-and-privilege-escalation-exploit/
Microsoft BitLocker-protected drives can now be opened with just some files on a USB stick — YellowKey zero-day exploit demonstrates an apparent backdoor | Tom's Hardware
https://www.tomshardware.com/tech-industry/cyber-security/microsoft-bitlocker-protected-drives-can-now-be-opened-with-just-some-files-on-a-usb-stick-yellowkey-zero-day-exploit-demonstrates-an-apparent-backdoor
Nightmare-Eclipse previously published two Windows Defender-related privilege escalation exploits in April 2026, making this his third such publication. This latest exploit, 'YellowKey,' reportedly allows for unrestricted access to protected volumes by physically accessing a Windows device with BitLocker protection enabled and exploiting the Windows Recovery Environment.
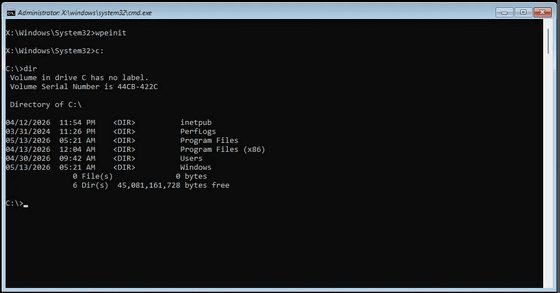
Yellow Key is a vulnerability where, if an attacker physically accesses a target PC and boots into the Windows Recovery Environment, certain files placed on a USB drive can trigger a process that opens a command line allowing access to a protected volume without entering a BitLocker recovery key. In other words, this vulnerability is not about 'mathematically breaking encryption,' but rather 'exploiting the target device's own recovery environment to make the protected drive accessible.'

The affected versions are Windows 11, Windows Server 2022, and Windows Server 2025, but Windows 10 is not affected. Nightmare-Eclipse claims that the component related to this issue exists in the Windows Recovery Environment and behaves differently from the component of the same name in a normal Windows environment, making it 'feel like a backdoor.'
Technology media outlet Tom's Hardware has confirmed that YellowKey works in-house, reporting that it was able to access BitLocker-protected drives without requiring any key input. They also point out that the behavior is unusual, going beyond a simple vulnerability, including the fact that related files disappear from the USB drive after the exploit is executed.
Another zero-day vulnerability, 'GreenPlasma,' is a privilege escalation vulnerability targeting CTFMON.exe, a Windows text input-related process. According to the security news site Cybernews, the published proof of concept is an incomplete version lacking the final element to obtain a complete SYSTEM shell, but it suggests that understanding the mechanism could lead to full privilege escalation.
Tom's Hardware points out that the impact of this newly discovered vulnerability is significant because BitLocker is widely used in Windows 11 environments. While BitLocker's key is stored in the TPM , meaning the drive cannot be immediately opened by simply transferring it to another PC, they explain that it could pose a serious risk if the device itself is stolen.
Nightmare-Eclipse has indicated that he may continue to disclose vulnerabilities due to his conflict with Microsoft, and has warned that 'the next Patch Tuesday will be a big surprise.'
Related Posts:







