Malware found in 'CPU-Z' and 'HWMonitor,' distribution site CPUID reports being hacked.
CPUID, a company that distributes software for benchmarking and monitoring Windows and Android devices, has been hacked, and malware was found to have been embedded in its CPU-Z software, which retrieves and displays CPU information on devices, and HWMonitor, which monitors hardware. CPUID has acknowledged that the breach lasted for approximately six hours, but has reported that the issue has been fixed.
CPUID hacked to deliver malware via CPU-Z, HWMonitor downloads
HWMonitor and CPU-Z developer CPUID breached by unknown attackers — cyberattack forced users to download malware instead of valid apps for six hours | Tom's Hardware
https://www.tomshardware.com/tech-industry/cyber-security/hwmonitor-and-cpu-z-developer-cpuid-breached-by-unknown-attackers-cyberattack-forced-users-to-download-malware-instead-of-valid-apps-for-approximately-six-hours
Security PSA: Popular Tools CPU-Z and HWMonitor Were Briefly Compromised | TechPowerUp
https://www.techpowerup.com/348138/security-psa-popular-tools-cpu-z-and-hwmonitor-were-briefly-compromised
The first person to point out this problem appears to be engineer Chris Titus. Although he mistakenly names the software in his post, he is reporting that software distributed by CPUID is infected with malware. ' HWInfo (HWiNFO) ' is hardware information acquisition software and is not distributed by CPUID.
HWInfo and CPU-Z both compromised. Millions about to be PWNED!
— Chris Titus Tech (@christitustech) April 10, 2026
CPU Z: https://t.co/cGVLSVUIX6
HW Monitor: https://t.co/4Puwc5EheK
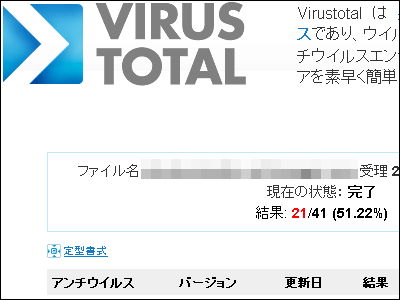
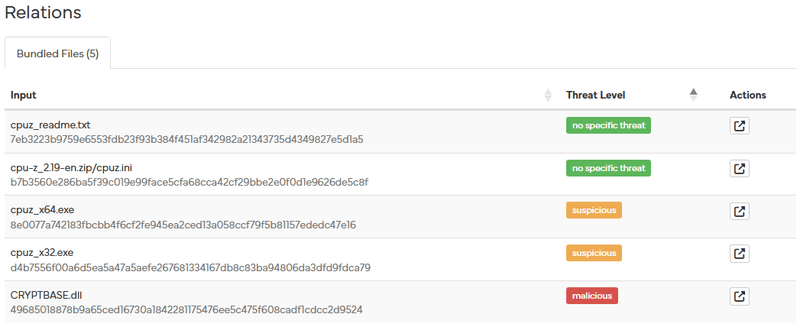
Titus shows the scan results for 'cpu-z_2.19-en.zip' from the malware scanning service HYBRID ANALYSIS.
Free Automated Malware Analysis Service - powered by Falcon Sandbox
https://hybrid-analysis.com/sample/eff5ece65fb30b21a3ebc1ceb738556b774b452d13e119d5a2bfb489459b4a46
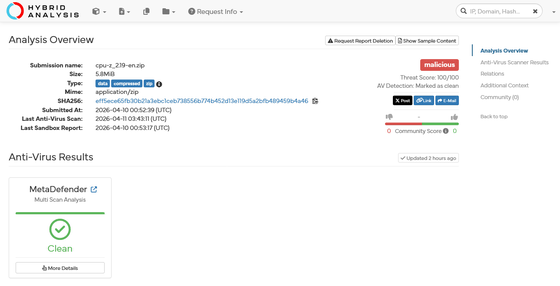
According to this information, among the included files, the executable files 'cpuz_x64.exe' and 'cpuz_x32.exe' are suspected of being infected, and 'CRYPTBASE.dll' has been confirmed to be infected.
VX UNDERGROUND, which provides a repository of malware files, has pointed out, in addition to Titus's information, that the malware being distributed is not commonplace malware, but a Trojan horse with means to evade EDR (Endpoint Detection and Response) and antivirus mechanisms. Based on the domains included in the binaries, the attackers are the same group that impersonated FileZilla in March 2026.
Mr. Titus Tech is correct. cpuid-dot-com is indeed delivering malware right now.
— vx-underground (@vxunderground) April 10, 2026
As I began poking this with I stick I discovered this is not your typical run-of-the-mill malware. This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs… https://t.co/ubkXmG7LKV pic.twitter.com/jPlAMmpijN
According to VX UNDERGROUND, the ultimate goal of this malware is to steal data, primarily browser credentials, and they 'have seriously worked on countermeasures and made some smart decisions during payload development.' Although it has some shortcomings, such as failing to implement emulation countermeasures and reusing the same C2 server used in the FileZilla incident to remotely control infected devices, it is still a fairly good piece of malware and has been rated 'B-'.
Yeah, so pretty much this https://t.co/Mwm1F8xKWT malware is a pain in the ass. I'd have to spend a good bit of time trying to bonk it with a stick and reconstruct some of it. Whoever developed this malware actually cares about evasion and made some intelligent decisions when… pic.twitter.com/XDJEhN4FDe
— vx-underground (@vxunderground) April 10, 2026
Samuel Dumelmeester of CPUID issued a statement saying, 'While the investigation is ongoing, it appears that a sub-function (basically the side API) was compromised for approximately six hours between April 9th and 10th, resulting in malicious links being randomly displayed on the main website (signed original files were not compromised). The compromise has been detected and corrected. We apologize for any inconvenience caused. We have done our best to resolve the issue.'
Here is the small statement I sent to everyone... 😓
— Doc TB (@d0cTB) April 10, 2026
Hi,
Investigations are still ongoing, but it appears that a secondary feature (basically a side API) was compromised for approximately six hours between April 9 and April 10, causing the main website to randomly display… https://t.co/ZfHRoWwkOM
Related Posts: