A zero-day vulnerability in Adobe Reader was exploited for several months.
Security researchers have reported the discovery of a zero-day vulnerability in Adobe Reader , Adobe's PDF viewing software, which is believed to be being exploited. Opening a malicious PDF file that exploits this vulnerability could lead to information theft or even computer hijacking.
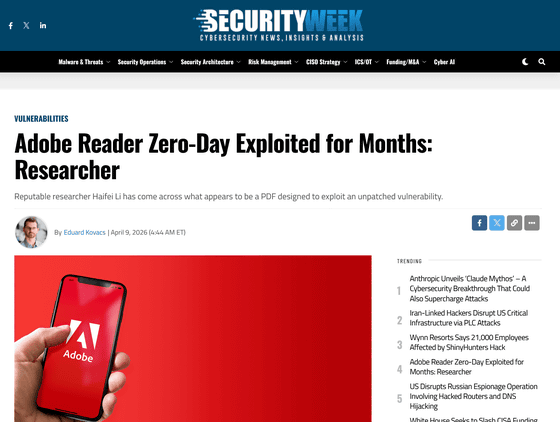
Adobe Reader Zero-Day Exploited for Months: Researcher - SecurityWeek
https://www.securityweek.com/adobe-reader-zero-day-exploited-for-months-researcher/
Old Adobe Reader zero-day uses PDFs to size up targets • The Register
https://www.theregister.com/2026/04/09/monthsold_adobe_reader_zeroday_uses/
Haifei Li, a security researcher who has worked at companies such as Microsoft and McAfee, is the founder and developer of Expmon , a sandbox-based system designed to detect file-based zero-day vulnerabilities and other exploits. Research using Expmon revealed a vulnerability in Adobe Reader that could be used to open malicious PDF files, potentially leading to attacks that collect and leak various types of information.
In addition, Lee stated in his X post that 'it appears the threat actor behind this Adobe Reader zero-day attack was not simply collecting local information, but was actually delivering additional exploits,' and called on the cybersecurity community to conduct further analysis.
Dear security community/researchers, I'd really like to call to look at this https://t.co/BuvZtpBChe , this information shows that the threat actors behind this Adobe Reader 0day attack was not just collecting local information but was really delivering additional exploits, need…
— Haifei Li (@HaifeiLi) April 8, 2026
Threat intelligence analysts who analyzed the attack pointed out that the malicious PDF file contained a message in Russian that referenced current events in Russia's oil and gas sector.
Apparent #0day in Adobe Reader has been observed in the wild. Seems to exploit part of Adobe Readers JavaScript engine. Documents observed contain Russian language lures and refer to issues regarding current events related to the oil and gas industry in Russia. https://t.co/QRu63fuAP4
— Gi7w0rm (@Gi7w0rm) April 8, 2026
The 'PDF exploit attack,' which takes advantage of a vulnerability in Adobe Reader, uses a malicious PDF file that executes immediately upon opening, requiring no clicks other than viewing the file, and is considered potentially difficult to defend against even in the latest environments. The attack relies on highly obfuscated JavaScript that executes as soon as the PDF is launched, using APIs built into Adobe Acrobat to retrieve information from the machine, such as local file and system details, and send it to a server controlled by the attacker.
Lee explained, 'The initial stage of an attack is basically reconnaissance, where the attacker obtains OS information, language settings, file paths, etc., to identify the target environment. If the attacker determines that the environment is useful, they obtain the payload for the second stage and execute it inside Adobe Reader. At this stage, the situation can escalate further, potentially leading to remote code execution or escaping from the sandbox. This mechanism allows attackers to collect user information, steal local data, and launch future attacks. If the target meets the attacker's criteria, the attacker may exploit additional vulnerabilities to carry out the attack.'
According to Lee, a sample of the PDF exploit attack was uploaded to VirusTotal, a website that scans files and websites for malware, on November 28, 2025, and the vulnerability may have been exploited for at least four months until it was discovered in March 2026. As of the time of writing, Adobe has not issued an official statement, and no fix patch for Adobe Reader has been released, so security researchers are urging users who have a habit of opening PDFs from unknown sources to be careful.
Related Posts: