BrowserGate is a research project that claims that every time you access LinkedIn, your PC is being illegally searched.

The business-focused social networking service LinkedIn is collecting information by searching for software installed on users' PCs, according to the research project BrowserGate . BrowserGate states that the collected data is being sent to LinkedIn's servers and to third-party companies, including cybersecurity firms in the United States and Israel.
BrowserGZ
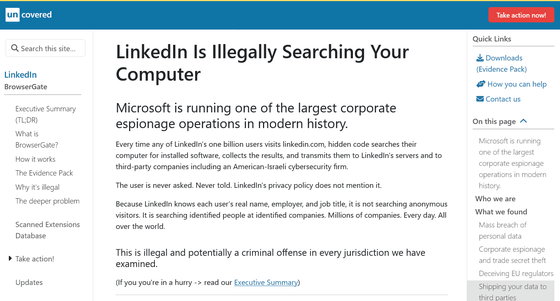
Fairlinked eV, a group comprised of LinkedIn's commercial users, claims to be collecting evidence of illegal scanning practices by LinkedIn on behalf of business professionals and companies that use LinkedIn, companies that invest in the platform, and toolmakers that develop products for LinkedIn. BrowserGate is Fairlinked eV's investigative project and campaign aimed at documenting LinkedIn's corporate espionage and data breach scandals, providing information to the public and regulators, and raising funds for the legal action needed to stop them.
According to research published by BrowserGate, when users access a LinkedIn page, specific code is executed on their browser, and information about installed software and browser extensions is collected. BrowserGate points out that LinkedIn scans for extensions that identify users as Muslim, extensions that reveal their political leanings, extensions built for users with neurodevelopmental disorders, and job-seeking tools that expose individuals secretly seeking employment on a platform where current employers can view their profiles, and then reveals the religious beliefs, political opinions, disabilities, and job-seeking status of identified individuals.
According to BrowserGate, LinkedIn has access to users' real names, workplaces, and job titles, which could mean it's linking data on specific individuals working at specific companies, as well as information like 'which companies are using which competitor products.' Fairlinked eV criticized LinkedIn for not providing any consent, disclosure, or legal basis for this information, and for making no mention of these scans in its privacy policy.

Furthermore, BrowserGate's investigation report indicates that the collected data is being sent not only to LinkedIn's servers but also to several external companies. This is said to include 'HUMAN Security,' a US-Israeli joint venture cybersecurity company, but the purpose for which the data is being shared remains unclear.
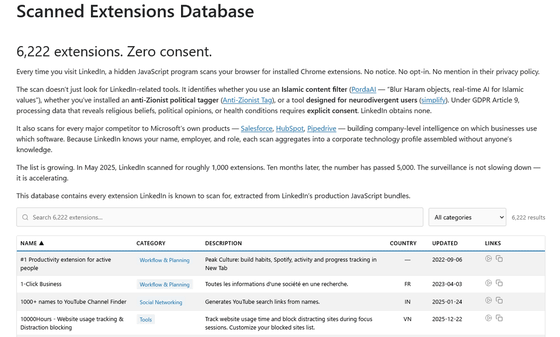
BrowserGate has published evidence on the following page. They state that any developer can check what is being scanned on their PC by opening linkedin.com in Chrome, opening the developer tools, looking for the JavaScript bundle, and then searching for the ID of any Chrome extension.
The Evidence Pack | BrowserGate
https://browsergate.eu/the-evidence-pack/
BrowserGate argues that such data collection may violate the EU's General Data Protection Regulation (GDPR) and California's Consumer Privacy Act (CCPA). In particular, they point out that processing data without explicit consent may be illegal if 'special categories of personal data,' such as religion, politics, or health status, can be inferred from the extension's information.
BrowserGate also stated that 'this is not just a privacy violation,' pointing out that the core of the problem extends beyond LinkedIn alone. They argue that scanning browser extensions without consent raises concerns about individual privacy, and since LinkedIn includes names, workplaces, job titles, and departments, 'this is not a privacy violation, it's corporate espionage.'
Scanning technologies like those used by LinkedIn are sometimes employed for purposes such as preventing misuse and detecting bots, and at the time of writing, there is no clear explanation from LinkedIn regarding its reasons for implementing this system. In fact, one user on the social news site Hacker News pointed out , 'While I think the scanning itself is problematic, this behavior is seen on most websites that display advertising code, so I disagree with BrowserGate's exaggerated claims.' BrowserGate recommends that users search its database for the tools LinkedIn is scanning, request data from LinkedIn, or file complaints with data protection authorities. BrowserGate says it will continue its investigation, and attention is focused on the responses of regulatory authorities and LinkedIn's official response.
Related Posts:
in Web Service, Security, Posted by log1e_dh