The 'DarkSword' malware, an exploit capable of hacking hundreds of millions of iPhones, has been publicly leaked.

In March 2026, Google's threat intelligence group reported ' DarkSword ,' an exploit that compromises iOS devices by taking advantage of multiple zero-day vulnerabilities. TechCrunch, an IT news site, has reported that the latest version of the malware that runs DarkSword has been released to its source code repository on GitHub.
Someone has publicly leaked an exploit kit that can hack millions of iPhones | TechCrunch
https://techcrunch.com/2026/03/23/someone-has-publicly-leaked-an-exploit-kit-that-can-hack-millions-of-iphones/
DarkSword is an exploit that takes advantage of six different vulnerabilities present in iOS 18.4–18.7, aiming to extract a wide range of personal information, including credentials, from devices. Many cryptocurrency wallets are particularly targeted, and at least three different types of malware that execute DarkSword have been identified as of the time of writing.
Google and others discover 'DarkSword,' an exploit chain for iOS that uses six vulnerabilities - GIGAZINE

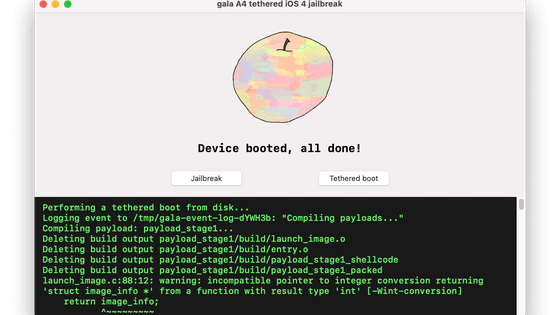
According to researchers, the malware that runs DarkSword can target iPhone users who haven't updated their iOS to the latest version. White hat hacker matteyeux also reported on X (formerly Twitter) that he was able to hack a 6th generation iPad mini running iPadOS 18.6.2 using a sample of the DarkSword malware circulating online.
Got kernel R/W on an iPad mini 6th gen running iOS 18.6.2 using the in the wild exploit chain darksword pic.twitter.com/zT2mc8TvbM
— matteyeux (@matteyeux) March 23, 2026
Matthias Freelingsdorff, co-founder of mobile security startup iVerify, said, 'This is bad, it can be easily exploited. It's no longer possible to contain DarkSword. We have to be prepared for criminals to start using it.'
A GitHub comment, presumably written by one of the developers of DarkSword, stated that 'this DarkSword malware reads forensically relevant files from iOS devices via HTTP and takes them outside. This payload should be injected into a process with file system access privileges.' This refers to stealing information from personal iPhones and iPads and sending the data via the internet to a server controlled by the attacker.

According to Freelingsdorf, the malware released on GitHub shares the same infrastructure as previously analyzed by iVerify , but the files themselves are slightly different. He also warned that because the files uploaded to GitHub are simple, consisting only of HTML and JavaScript, anyone can copy and paste them and immediately host them on a server.
According to Apple's own data , about a quarter of iPhone and iPad users are still using iOS versions older than 18, and TechCrunch says this 'likely impacts hundreds of millions of active iPhones and iPads.'
Apple spokesperson Sarah O'Rourke told TechCrunch, 'Apple is aware of a vulnerability that targets devices running older versions of its operating system, and we released an emergency update on March 11 for devices that cannot run the latest version of iOS. The most important thing to keep Apple products secure is to keep your software up to date.'
Related Posts:
in Software, Smartphone, Security, Posted by log1i_yk