Vulnerabilities have been discovered in IP-KVM systems from four manufacturers.

A vulnerability has been discovered in some models of IP-KVM, a device used to remotely access devices on a network, potentially allowing the devices to be compromised. Security firm Eclypsium has reported the details.
Your KVM is the Weak Link: How $30 Devices Can Own Your Entire Network - Eclypsium | Supply Chain Security for the Modern Enterprise
Researchers disclose vulnerabilities in IP KVMs from four manufacturers - Ars Technica
https://arstechnica.com/security/2026/03/researchers-disclose-vulnerabilities-in-ip-kvms-from-4-manufacturers/
According to Eclypsium, a total of nine IP-KVMs provided by four companies—GL-iNet, Angiet/Yeeso, Sipeed, and JetKVM—each have different vulnerabilities. The most serious vulnerability could allow attackers to gain root privileges without authentication or execute malicious code.
For example, GL-iNet's Comet RM-1 product has four vulnerabilities: 'insufficient firmware authenticity verification ( CVE-2026-32290 )', 'root access ( CVE-2026-32291 )', 'insufficient protection against brute-force attacks ( CVE-2026-32292 )', and 'insecure initial provisioning due to unauthenticated cloud connections ( CVE-2026-32293 )'. As of the time of writing, GL-iNet has fixed the latter two vulnerabilities, but plans to fix the first two.

Taking CVE-2026-32292 as an example, the lack of login rate limiting meant that authentication credentials could be determined by attempting thousands of logins per second.
Eclypsium stated, 'This is not a special vulnerability that can be found through months of reverse engineering. These are basic security measures that should be implemented as a matter of course in any network-connected device.'
Eclypsium reports that

Security expert HD Moore warned, 'The fundamental problem is that if KVM is compromised, it becomes easy to take over the systems connected to it, even if the systems themselves are secure against network attacks.'
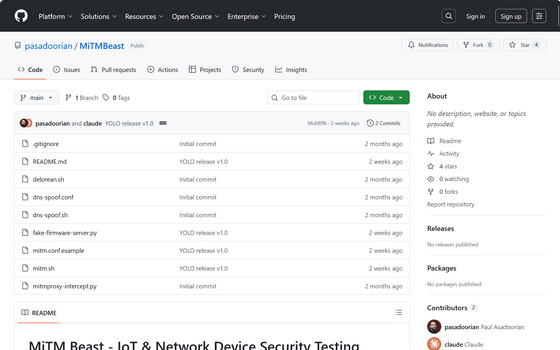
Eclypsium recommends that administrators scan their networks for any overlooked IP-KVMs. Eclypsium researcher Paul Assadrian has also released a scanning tool to identify problematic devices.
GitHub - pasadoorian/MiTMBeast · GitHub
Related Posts: